Having fun with TryHackMe again. So, here is the write up and guideline to pass this Biohazard challenge.

Room: https://tryhackme.com/room/biohazard
Level: Medium
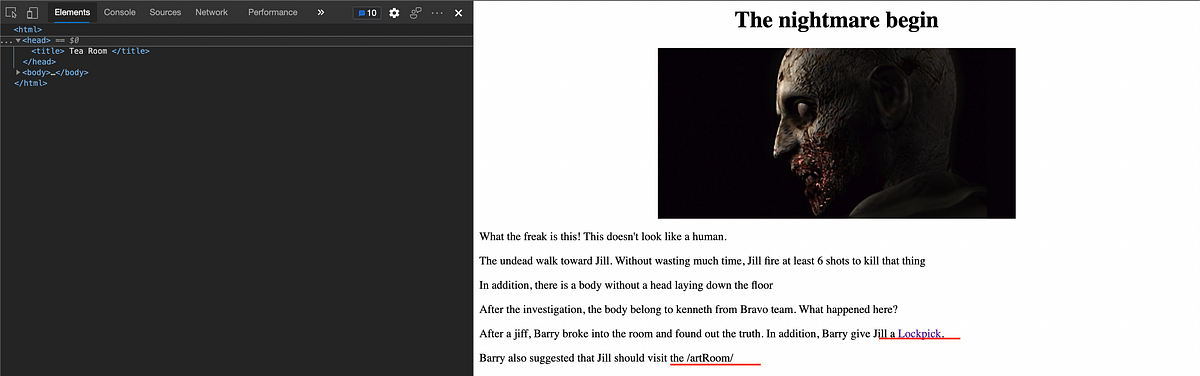
Task: A CTF room based on the old-time survival horror game, Resident Evil. Can you survive until the end?
Lets get started
As usual, start the machine and open the IP in browser

Its a “detective-like” game. Cool.. Lets proceed..
How many open ports?
# nmap -T4 -A -sS -sS -p- 10.10.X.X
21/tcp open ftp vsftpd 3.0.3
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 c9:03:aa:aa:ea:a9:f1:f4:09:79:c0:47:41:16:f1:9b (RSA)
| 256 2e:1d:83:11:65:03:b4:78:e9:6d:94:d1:3b:db:f4:d6 (ECDSA)
|_ 256 91:3d:e4:4f:ab:aa:e2:9e:44:af:d3:57:86:70:bc:39 (ED25519)
80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
|_http-server-header: Apache/2.4.29 (Ubuntu)
|_http-title: Beginning of the end
3 ports are open. The FTP cannot be access as anonymous. It’s okay..
What is the team name in operation?

Its Stars alpha team. Clearly stated in the main page. Done the introduction part. Now, The Mansion part…
The Mansion
The task is to collect all necessary items and advanced to the next level. Some of the doors are locked. Use the item flag to unlock the door.
First thing first, always open developer console because there’s always hint in the source code
What is the emblem flag?
Click “mansion” link and it open this page. Its a dead end

Inspect the code, there is a hidden path /diningRoom. Open the path

There is encrypted message in the code. Looks like base64.
# echo "the code" | base64 --decode
How about the /teaRoom/
It’s give another hidden path to be explore. Before that, the dining room have other link. Click the YES link

Okay.. Found the emblem flag. Next!
What is the lock pick flag?
Open the teaRoom/ path
Found the lock pick flag. Next!
What is the music sheet flag?
Proceed to /artRoom


Ok now found the list of available path map. Take a look at barRoom/ first

It’s locked. Using the lockpick flag,

Found another cipher.
NV2XG2LDL5ZWQZLFOR5TGNRSMQ3TEZDFMFTDMNLGGVRGIYZWGNSGCZLDMU3GCMLGGY3TMZL5
Doesn’t looks like base64 to me. Some kind of cipher family i think. Using cyberchef to test.

Its base32.. Found the music flag
What is the gold emblem flag?
Back to barRoom/ and enter the music flag

Found the gold emblem flag. Next!
What is the shield key flag?
Dead end. Looking to the map, lets open the diningRoom2F

Found another cipher. Looks like shift cipher. Using ROT13
Lbh trg gur oyhr trz ol chfuvat gur fgnghf gb gur ybjre sybbe. Gur trz vf ba gur qvavatEbbz svefg sybbe. Ivfvg fnccuver.ugzy

Decoded! It’s say to go down to the diningRoom again and visit the link given. Ok then,

It’s locked. It ask for emblem key. Either first emblem or gold emblem. Test both of them.
Now. There is another cipher
klfvg ks r wimgnd biz mpuiui ulg fiemok tqod. Xii jvmc tbkg ks tempgf tyi_hvgct_jljinf_kvc
Its not ROT13, referring to the hint, it might related to Vigenere Cipher. But vigenere cipher need a key. Just use the online cracker then,

Go to the /diningRoom/the_great_sheild_key.html and found the key. Next!
What is the blue gem flag?
Remember when trying to find the shield key?

It wrote something about blue gem locate also in the diningRoom. Lets visit the given link. Found the key. Next!
What is the FTP username?
Dead end. Looking to the map, lets open the tigerStatusRoom

Put the gem key and proceed. Found another cipher and related to FTP username
crest 1:S0pXRkVVS0pKQkxIVVdTWUpFM0VTUlk9 Hint 1: Crest 1 has been encoded twice
Hint 2: Crest 1 contanis 14 letters Note: You need to collect all 4 crests, combine and decode to reveal another path The combination should be crest 1 + crest 2 + crest 3 + crest 4. Also, the combination is a type of encoded base and you need to decode it
There is 4 crests need to be collected.
Lets check the galleryRoom

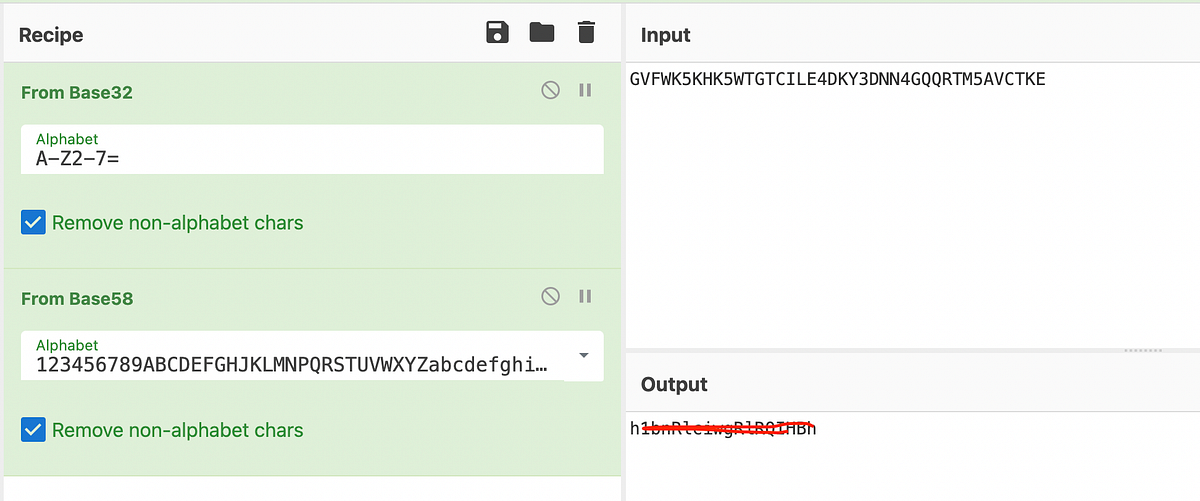
crest 2: GVFWK5KHK5WTGTCILE4DKY3DNN4GQQRTM5AVCTKE
Hint 1: Crest 2 has been encoded twice
Hint 2: Crest 2 contanis 18 letters
Found crest no 2.
Lets check the studyRoom
It’s locked. It needs the helmet symbol key which not yet to be found. Proceed to the armorRoom then
Enter the shield key from previous quest

crest 3:
MDAxMTAxMTAgMDAxMTAwMTEgMDAxMDAwMDAgMDAxMTAwMTEgMDAxMTAwMTEgMDAxMDAwMDAgMDAxMTAxMDAgMDExMDAxMDAgMDAxMDAwMDAgMDAxMTAwMTEgMDAxMTAxMTAgMDAxMDAwMDAgMDAxMTAxMDAgMDAxMTEwMDEgMDAxMDAwMDAgMDAxMTAxMDAgMDAxMTEwMDAgMDAxMDAwMDAgMDAxMTAxMTAgMDExMDAwMTEgMDAxMDAwMDAgMDAxMTAxMTEgMDAxMTAxMTAgMDAxMDAwMDAgMDAxMTAxMTAgMDAxMTAxMDAgMDAxMDAwMDAgMDAxMTAxMDEgMDAxMTAxMTAgMDAxMDAwMDAgMDAxMTAwMTEgMDAxMTEwMDEgMDAxMDAwMDAgMDAxMTAxMTAgMDExMDAwMDEgMDAxMDAwMDAgMDAxMTAxMDEgMDAxMTEwMDEgMDAxMDAwMDAgMDAxMTAxMDEgMDAxMTAxMTEgMDAxMDAwMDAgMDAxMTAwMTEgMDAxMTAxMDEgMDAxMDAwMDAgMDAxMTAwMTEgMDAxMTAwMDAgMDAxMDAwMDAgMDAxMTAxMDEgMDAxMTEwMDAgMDAxMDAwMDAgMDAxMTAwMTEgMDAxMTAwMTAgMDAxMDAwMDAgMDAxMTAxMTAgMDAxMTEwMDA=
Hint 1: Crest 3 has been encoded three times
Hint 2: Crest 3 contains 19 letters
Found the crest no 3.
Proceed to the last route from the map. The Attict
Ask for the same key as armorRoom. Enter the room

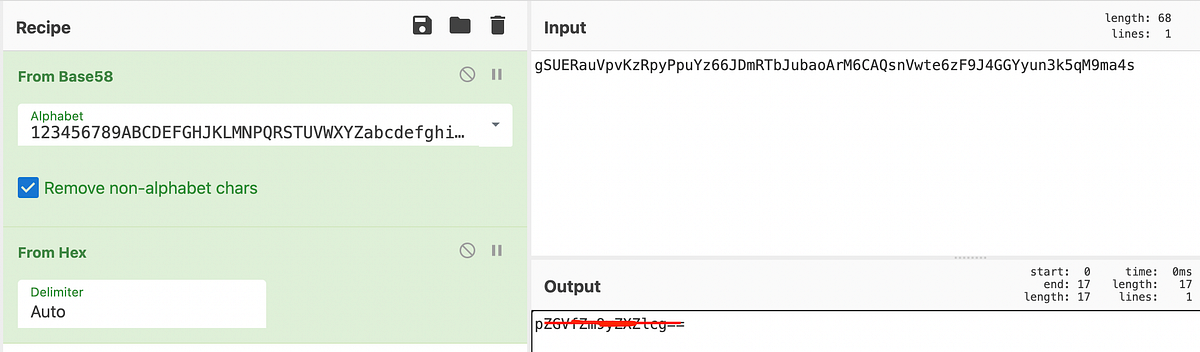
crest 4:
gSUERauVpvKzRpyPpuYz66JDmRTbJubaoArM6CAQsnVwte6zF9J4GGYyun3k5qM9ma4s
Hint 1: Crest 2 has been encoded twice
Hint 2: Crest 2 contanis 17 characters
Found all the crests. Lets take a look again
crest 1:S0pXRkVVS0pKQkxIVVdTWUpFM0VTUlk9 (E: 2x, 14 letters)
crest 2:GVFWK5KHK5WTGTCILE4DKY3DNN4GQQRTM5AVCTKE (E: 2x, 18 letters)
crest 3:
MDAxMTAxMTAgMDAxMTAwMTEgMDAxMDAwMDAgMDAxMTAwMTEgMDAxMTAwMTEgMDAxMDAwMDAgMDAxMTAxMDAgMDExMDAxMDAgMDAxMDAwMDAgMDAxMTAwMTEgMDAxMTAxMTAgMDAxMDAwMDAgMDAxMTAxMDAgMDAxMTEwMDEgMDAxMDAwMDAgMDAxMTAxMDAgMDAxMTEwMDAgMDAxMDAwMDAgMDAxMTAxMTAgMDExMDAwMTEgMDAxMDAwMDAgMDAxMTAxMTEgMDAxMTAxMTAgMDAxMDAwMDAgMDAxMTAxMTAgMDAxMTAxMDAgMDAxMDAwMDAgMDAxMTAxMDEgMDAxMTAxMTAgMDAxMDAwMDAgMDAxMTAwMTEgMDAxMTEwMDEgMDAxMDAwMDAgMDAxMTAxMTAgMDExMDAwMDEgMDAxMDAwMDAgMDAxMTAxMDEgMDAxMTEwMDEgMDAxMDAwMDAgMDAxMTAxMDEgMDAxMTAxMTEgMDAxMDAwMDAgMDAxMTAwMTEgMDAxMTAxMDEgMDAxMDAwMDAgMDAxMTAwMTEgMDAxMTAwMDAgMDAxMDAwMDAgMDAxMTAxMDEgMDAxMTEwMDAgMDAxMDAwMDAgMDAxMTAwMTEgMDAxMTAwMTAgMDAxMDAwMDAgMDAxMTAxMTAgMDAxMTEwMDA= (E: 3x, 19 letters)
crest 4: gSUERauVpvKzRpyPpuYz66JDmRTbJubaoArM6CAQsnVwte6zF9J4GGYyun3k5qM9ma4s (E: 2x, 17 letters) The combination should be crest 1 + crest 2 + crest 3 + crest 4. Also, the combination is a type of encoded base and you need to decode it
Here we go…


About 30 minutes to try and error each of the encoder in cyberchef. Lets see if it is correct if we combine it
RlRQIHVzZXXXX + h1bnRlciwgRlRXXXXX + c3M6IHlvdV9jXXXXXX + pZGVfZm9yZXZXXXXX = XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX
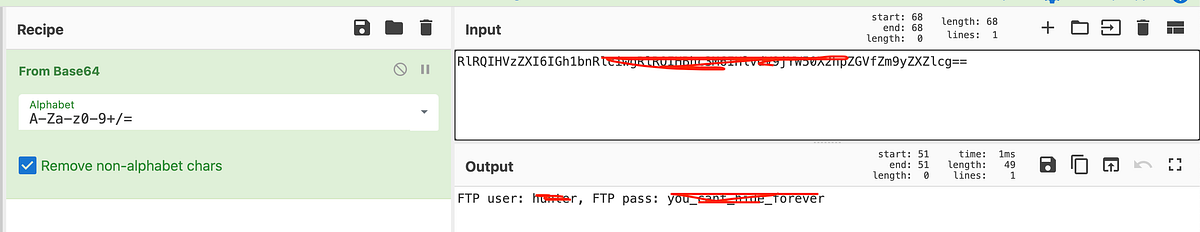
Found the FTP username and password. Finished the “The Mansion” task! 2 down 3 to go..
The guard house
After gaining access to the FTP server, i need to solve another puzzle. There is 5 files.
Where is the hidden directory mentioned by Barry?
Read the important.txt file
Jill, I think the helmet key is inside the text file, but I have no clue on decrypting stuff. Also, I come across a /*************/ door but it was locked. From,
Barry
Opening the hidden passage as written in the message

It’s locked. It needs the “helmet key” same as studyRoom/. But the helmet key file is locked with password.
Password for the encrypted file ?
There are 3 images represent the keys.
# binwalk 001-key.jpg 002-key.jpg 003-key.jpg Scan Time: 2021-05-31 10:12:48
Target File: ~/001-key.jpg
MD5 Checksum: 076b6a86ba92c75d366f0a18b505dcf8
Signatures: 411 DECIMAL HEXADECIMAL DESCRIPTION
--------------------------------------------------------------------
0 0x0 JPEG image data, JFIF standard 1.01 Scan Time: 2021-05-31 10:12:48
Target File: ~/002-key.jpg
MD5 Checksum: 060af11c5617fbc4fba1760f0dd52a0d
Signatures: 411 DECIMAL HEXADECIMAL DESCRIPTION
--------------------------------------------------------------------
0 0x0 JPEG image data, JFIF standard 1.01 Scan Time: 2021-05-31 10:12:48
Target File: ~/003-key.jpg
MD5 Checksum: 5c407556b6956ba74cda5ce98f8acf08
Signatures: 411 DECIMAL HEXADECIMAL DESCRIPTION
--------------------------------------------------------------------
0 0x0 JPEG image data, JFIF standard 1.01
1930 0x78A Zip archive data, at least v2.0 to extract, uncompressed size: 14, name: key-003.txt
2124 0x84C End of Zip archive, footer length: 22
003-key.jpg have archive data in it. Unzip the 003-key.jpg,
# unzip 003-key.jpg
Archive: 003-key.jpg
warning [003-key.jpg]: 1930 extra bytes at beginning or within zipfile
(attempting to process anyway)
inflating: key-003.txt # cat key-003.txt
3aXRoXXXXXXXXXX
Found the key no 3. Lets check the key 1 and 2.
# strings 001-key.jpg 002-key.jpg
...
... 5fYmVfZGVzXXXXXX
...
Found key no 2. None for key no 1. Seem hidden.. Using online stega decoder, found the no 1. Combine the key and using cyberchef to decode,
Key1+key2+key3 = XXXXXXXXcan_be_destroyXXXXXXXXXX
Found the password. Use it to decrypt the gpg file.
# gpg -d helmet_key.txt.gpg
gpg: AES256.CFB encrypted data
gpg: encrypted with 1 passphrase
helmet_key{XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX}
Now, we found the helmet key.
The Revisit
There are places you have explored before but yet to access.
What is the SSH login username?
Unlock the closet room using the helmet key.

There are 2 links, Link 1 shows
wpbwbxr wpkzg pltwnhro, txrks_xfqsxrd_bvv_fy_rvmexa_ajk
Link 2 shows
SSH password: XXXXXXXXXXXXX
Cracking using online vigenere Solver,

Some kind of other user and password. Lets test it for SSH
# ssh weasker@10.10.X.X # ls
Desktop weasker_note.txt
There is some note left by the Weasker
# cat weasker_note.txt
Weaker: Finally, you are here, Jill.
Jill: Weasker! stop it, You are destroying the mankind. Weasker: Destroying the mankind? How about creating a 'new' mankind. A world, only the strong can survive.
Jill: This is insane. Weasker: Let me show you the ultimate lifeform, the Tyrant. (Tyrant jump out and kill Weasker instantly)
(Jill able to stun the tyrant will a few powerful magnum round) Alarm: Warning! warning! Self-detruct sequence has been activated. All personal, please evacuate immediately. (Repeat) Jill: Poor bastard
Keep digging,
# ls -al /home
drwxr-xr-x 4 hunter hunter 4096 Sep 19 2019 hunter
drwxr-xr-x 8 umbrella_guest umbrella 4096 Sep 20 2019 XXXXXXXXX
drwxr-xr-x 9 weasker weasker 4096 Sep 20 2019 weasker
Found the SSH login user
What is the SSH login password?
Found at link no 2
Who the STARS bravo team leader?
Clearly stated in the closet room
Underground laboratory
Time for the final showdown. Can you escape the nightmare?
Browsing the server using weasker ssh,
Where you found Chris
# ls -al /home/XXXXXXXX/
...
...
drwxr-xr-x 11 umbrella_guest umbrella 4096 Sep 19 2019 .config
-rw-r--r-- 1 umbrella_guest umbrella 26 Sep 19 2019 .dmrc
drwx------ 3 umbrella_guest umbrella 4096 Sep 19 2019 .gnupg
drwxr-xr-x 2 umbrella_guest umbrella 4096 Sep 20 2019 .jailcell
drwxr-xr-x 3 umbrella_guest umbrella 4096 Sep 19 2019 .local
-rw-r--r-- 1 umbrella_guest umbrella 807 Sep 19 2019 .profile
...
There is a weird folder. Open it
# ls -al .jailcell
....
-rw-r--r-- 1 umbrella_guest umbrella 501 Sep 20 2019 chris.txt
.... # cat chris.txt
Jill: Chris, is that you? Chris: Jill, you finally come. I was locked in the Jail cell for a while. It seem that weasker is behind all this.
Jil, What? Weasker? He is the traitor?
Chris: Yes, Jill. Unfortunately, he play us like a damn fiddle.
Jill: Let's get out of here first, I have contact brad for helicopter support.
Chris: Thanks Jill, here, take this MO Disk 2 with you. It look like the key to decipher something.
Jill: Alright, I will deal with him later.
Chris: see ya. MO disk 2: albert
Alright now we found where is Chris located
Who is the traitor?
Weasker is the traitor and i’m using his account 😏
The login password for the traitor?
Already found it
The name of the ultimate form?
Also already found from the Weasker’s note
The root flag?
# sudo -l
Matching Defaults entries for weasker on umbrella_corp: env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin User weasker may run the following commands on umbrella_corp: (ALL : ALL) ALL
Oh! there are multiple way. Referring to GTFObins, using the env_reset

# sudo env /bin/sh
# ls /root
root.txt
# cat /root/root.txt In the state of emergency, Jill, Barry and Chris are reaching the helipad and awaiting for the helicopter support. Suddenly, the Tyrant jump out from nowhere. After a tough fight, brad, throw a rocket launcher on the helipad. Without thinking twice, Jill pick up the launcher and fire at the Tyrant. The Tyrant shredded into pieces and the Mansion was blowed. The survivor able to escape with the helicopter and prepare for their next fight. The End flag: XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX
Finished! Very long quest…
Happy Hacking ~~~~


