The Growing Threat of Malware Apps and the Need for a Safer Authentication Method, More Secure User Experiences

In the ever-evolving world of cybersecurity, businesses and consumers are constantly playing catch-up with innovative and relentless cybercriminals. Recent cyberattacks have seen malicious software sneak onto customers’ mobile apps, reading incoming SMS messages, including those containing one-time passwords (OTPs). This alarming development has led to a drastic increase in unauthorized account takeovers, causing significant distress and financial losses.
As a developer with first-hand experience in these digital battlegrounds, I understand the urgency of addressing this issue. Fortunately, there’s a promising solution on the horizon: Push Notification OTPs. Let’s take a deep dive into this new technology, its advantages and how we can implement it effectively to safeguard our digital assets.
The Threat of Malware Apps
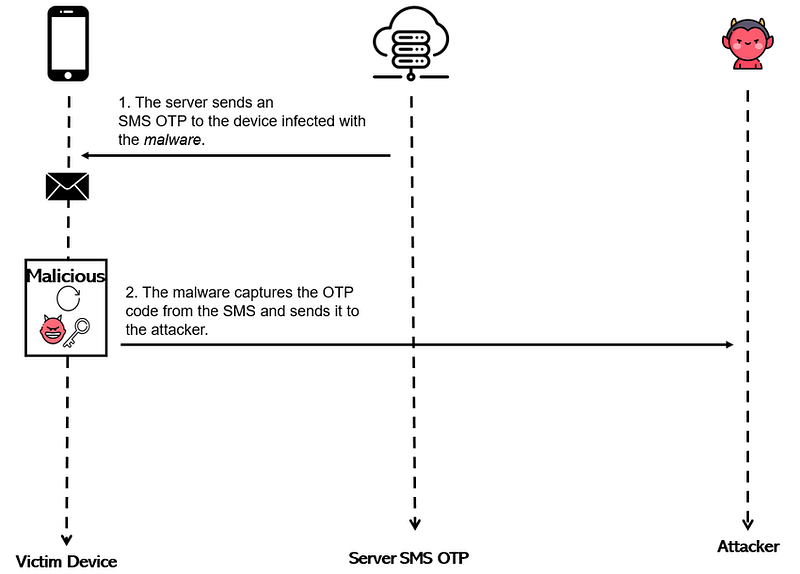
First, let’s delve into the crux of the matter: the rise of malicious apps. These applications are designed to infiltrate a user’s mobile device and siphon off sensitive information, including OTPs. As two-factor authentication (2FA) has become more prevalent, cybercriminals have adapted their strategies to circumvent this additional layer of security. The OTPs, which are supposed to act as a second barrier, are being intercepted, leading to a surge in unauthorized account takeovers.
According to Securelist, in 2022, malware was used in most mobile attacks (67.78%). The shares of attacks that used Adware and RiskWare-type applications had increased to 26.91% from 16.92% in 2021 and to 5.31% from 2.38% in 2021, respectively.
This is not a hypothetical threat, but a real, tangible danger that requires immediate attention and action.
6.2K views, 159 likes, 1 loves, 22 comments, 218 shares, Facebook Watch Videos from Tan Aik Keong: A real demo on how…www.facebook.com
The Limitations of SMS OTPs
While SMS OTPs have served us well over the years, their susceptibility to interception exposes the inherent flaws in this system. There are two primary weak points:
- Network Vulnerabilities: SMS messages are transmitted over cellular networks, which can be compromised. Techniques such as SIM swapping and man-in-the-middle attacks have been used to intercept OTPs.
- Device Vulnerabilities: Once an SMS reaches a device, it is no longer secure. Malware apps can read these messages and relay the OTPs back to the cybercriminals.
Push Notification OTPs: The New Frontier in Cybersecurity
As we grapple with these cyber threats, there’s a clear need for a more secure OTP delivery method. Push Notification OTPs can be the answer. These notifications are encrypted end-to-end, meaning they cannot be intercepted during transmission. Moreover, they can be configured to be displayed only within the secure confines of a specific app, shielding them from prying malware on a user’s device. Here’s why this method is superior:
- Encrypted communication: Push notifications are sent over HTTPS, meaning the data is encrypted during transit. This encryption makes it far more challenging for cybercriminals to intercept and read the OTPs.
- App-specific: Push notifications are app-specific. They are only visible and accessible to the intended app, which further reduces the chances of interception.
- User interaction required: Push Notification OTPs usually require user interaction to be viewed, adding an additional layer of security.
- No reliance on network providers: Unlike SMS messages, push notifications don’t rely on network providers, which often have varying levels of security.
- Enhanced Security: As mentioned, the end-to-end encryption and app-specific display offer an additional layer of security.
- Cost-Effective: Unlike SMS, which incurs per-message costs, push notifications are generally included in the app platform’s fee.
- Immediate Delivery: Push notifications typically arrive faster than SMS, providing a smoother user experience.
- Rich Content: Push notifications can include more than just text, allowing for a more engaging and informative user experience.
Implementing Push Notification OTPs
Implementing Push Notification OTPs requires a certain level of technical knowledge. Here, we will outline the steps in the process:
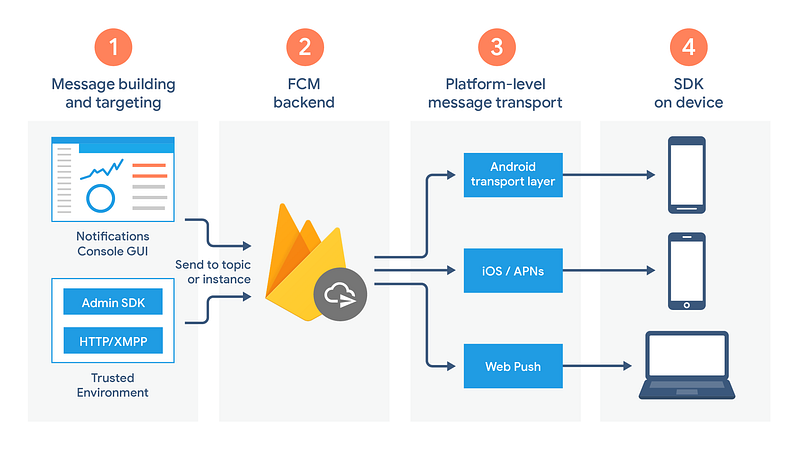
- Choose a Push Notification Service: There are several reputable push notification services available, including Firebase Cloud Messaging (FCM), OneSignal and Amazon Simple Notification Service (SNS).
- Configure the Service: Once you’ve chosen a service, you need to configure it for your app. This process usually involves obtaining a Server Key and Sender ID (for FCM) or an Access Key and Secret Key (for SNS).
- Implement the Service in Your App: Now, you need to incorporate the service into your app’s code. This process involves adding specific codes into your app to handle the receipt and display of push notifications.
- Test the Implementation: After implementing the service, test it thoroughly to ensure that OTPs are being sent and received correctly.
Remember, the key to a secure implementation is keeping your keys and IDs secret. If they fall into the wrong hands, they could be used to send unauthorized push notifications.
Overcoming Challenges: User Adoption and Technical Hurdles
Implementing Push Notification OTPs is not without its challenges. Let’s look at two primary hurdles:
- User adoption: Like any new technology, user adoption can be a stumbling block. While push notification OTPs offer superior security, users may initially resist the change. To counter this, education is crucial. Users must understand why the change is being made and how it will enhance their security.
- Technical implementation: Implementing a new system can be challenging, especially when it involves changes to an app’s code. Developers must ensure that push notifications are implemented correctly and that they work across different devices and operating systems. Thorough testing is essential to identify and rectify any issues early.
Conclusion
The alarming rise in cyberattacks, particularly those leveraging the interception of SMS OTPs, underscores the urgency of finding robust, innovative solutions to safeguard our digital spaces. Push Notification OTPs, with their enhanced security features, offer a promising alternative that can significantly reduce the risk of account takeovers.
However, the adoption of this technology involves overcoming a few challenges, including user resistance and technical implementation issues. By addressing these challenges head-on through education and thorough testing, we can build a more secure digital world.
The fight against cybercrime is an ongoing one and it’s a fight we’re all a part of. Stay informed, stay secure and remember, every step we take towards better security practices is a step towards a safer internet for all.
As we continue to wage this battle against cybercriminals, it is essential that we not only react to their tactics but proactively seek out and implement stronger, more effective defenses. The switch to Push Notification OTPs is not just a necessary move; it’s a strategic one, aimed at staying one step ahead in the ever-evolving cybersecurity landscape.
Let’s embrace this change, for it signals a new era in cybersecurity — an era where we are not mere bystanders in the face of cyber threats but active participants in designing and implementing solutions that protect our digital lives.
Found this helpful?
If this article saved you time or solved a problem, consider supporting — it helps keep the writing going.
Originally published on Medium.
View on MediumYou might also like

The Audit Asked If We Had SSDLC. I Had to Google It. Here Is What It Means.
April 6, 2026
The Livewire v3 RCE That Broke the Magic: Understanding CVE-2025–54068
April 6, 2026